Wechat Video Downloader Robot May 2026
Secure, scalable, and game-changing authentication for your applications. Get started in minutes with our powerful APIs and SDKs.

Secure, scalable, and game-changing authentication for your applications. Get started in minutes with our powerful APIs and SDKs.

Integrate into any programming language

A comprehensive suite of integrated tools for authentication, monetization, and user engagement.
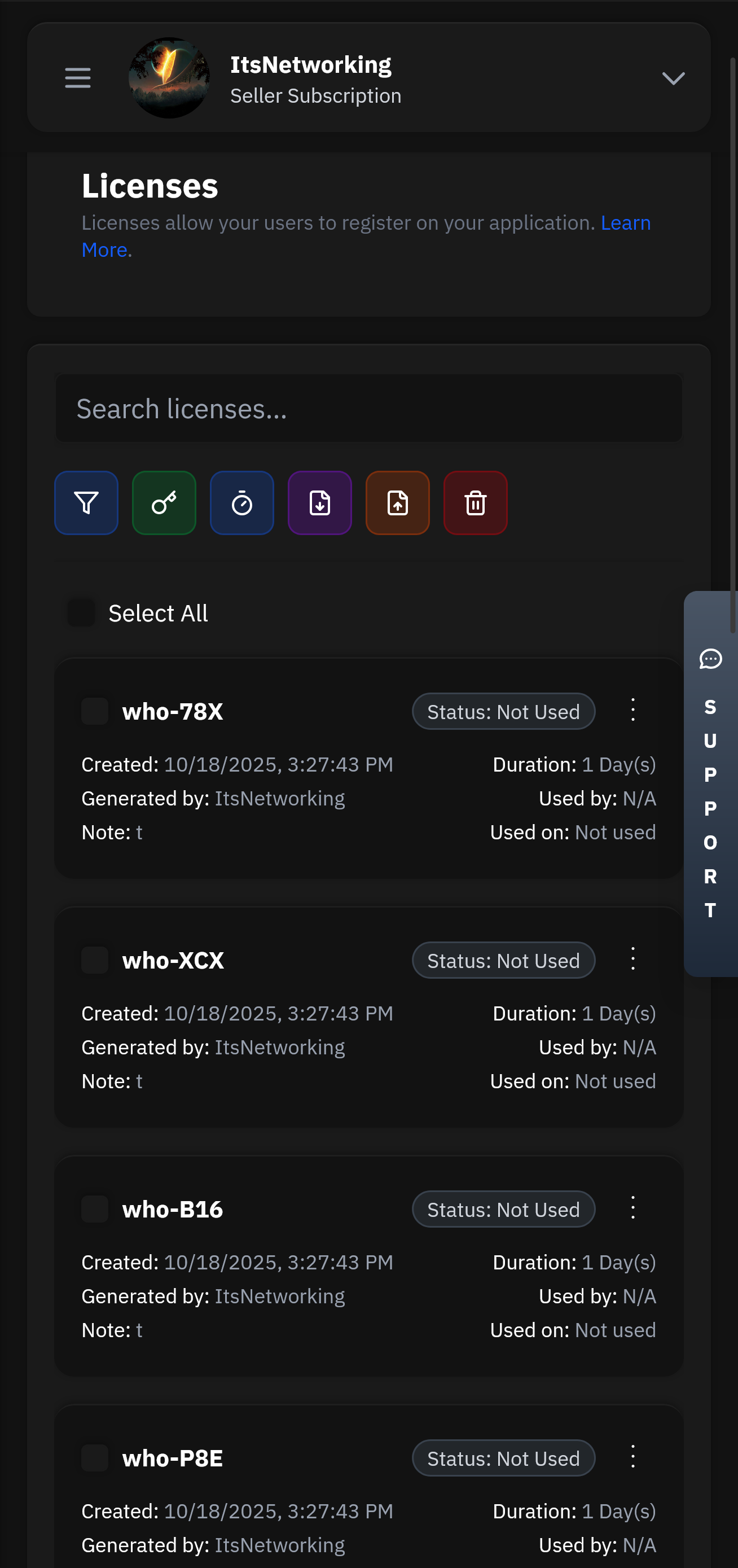
Create and manage user licenses with flexible expiration, trial, and subscription options.
Our lightning-fast infrastructure ensures your authentication requests are processed in under 50ms globally. With 99.99% uptime and redundant systems, your users will never experience delays.
Manage your applications remotely with our powerful Seller API. Update licenses, ban users, modify subscriptions, and monitor usage from anywhere in the world with full administrative control.
Built on a serverless architecture that automatically scales to handle millions of requests. Our global edge network ensures low latency and high availability across 300+ locations worldwide.
There's no question as to why we are the best choice for your business and one of the most used Authentication services.
Head over to our register page to create your account.
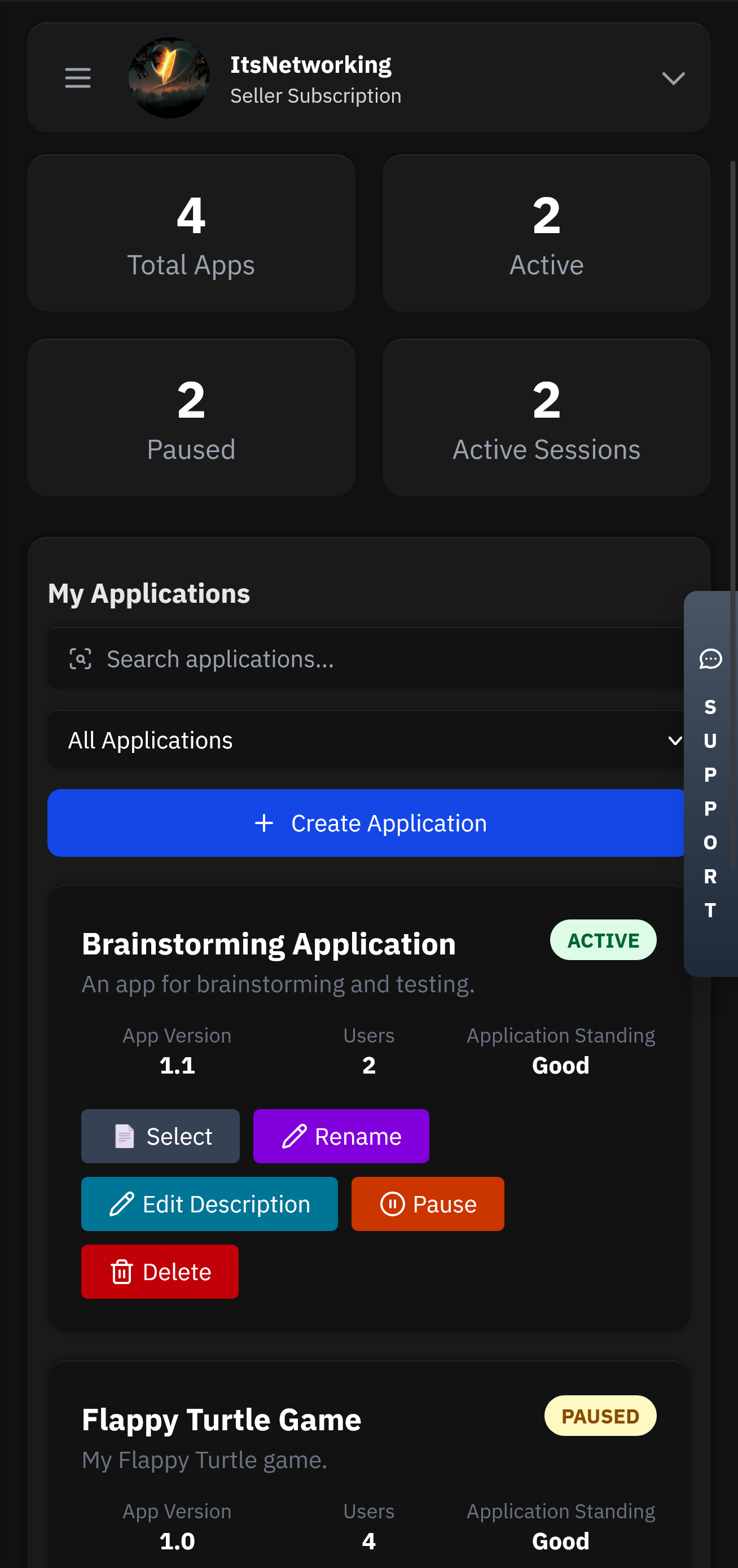
Applications will be the heart of your service. This is where all your users, licenses, chats and more will be stored.
Head over to our GitHub to find our examples and client API files. Simply follow the steps and have authentication up in less than 5 minutes.
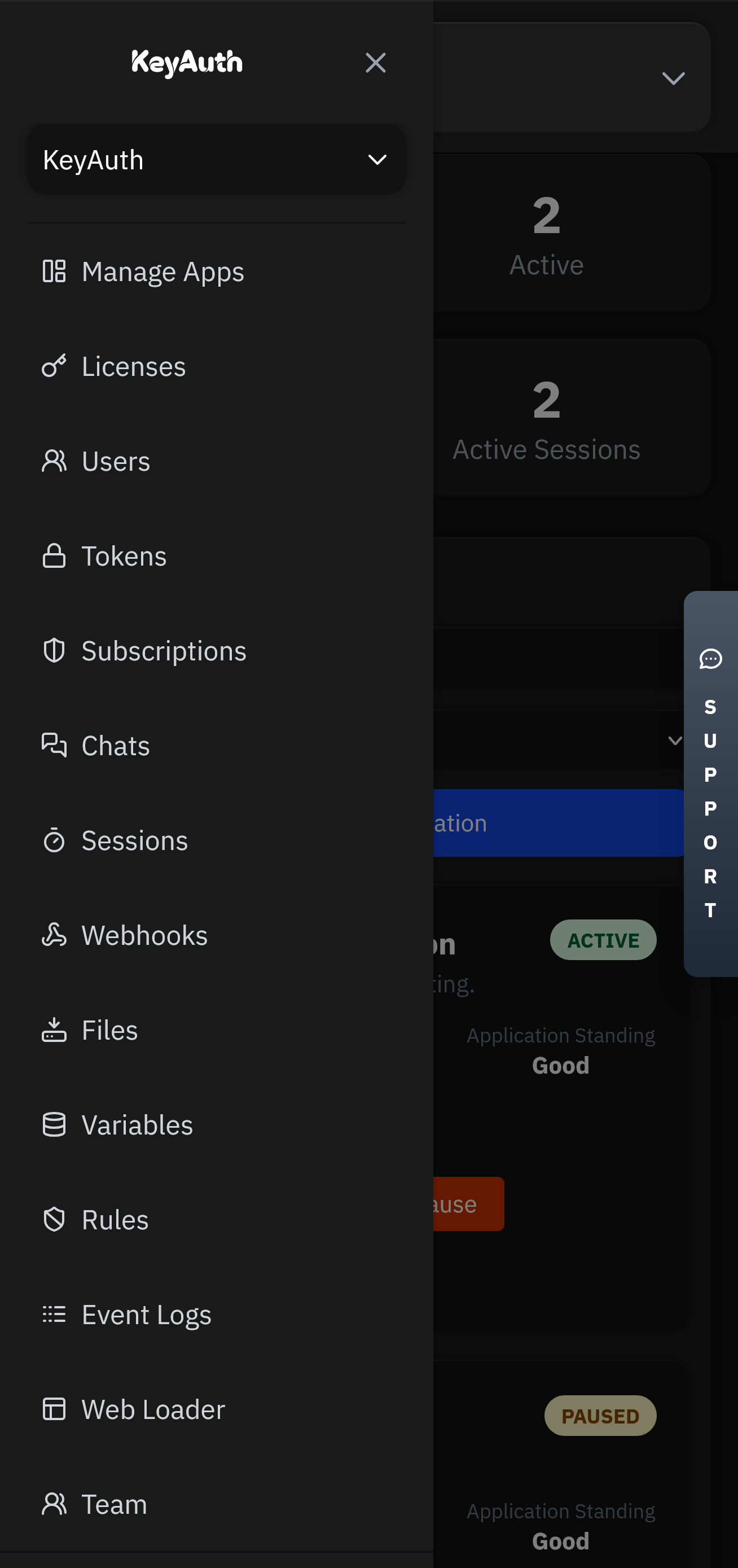
Control your application from anywhere using our mobile app. Manage licenses, chat with users, and view analytics directly from your phone or tablet.
Flexible options for teams of all sizes.
In environments where content can be retroactively censored or removed (by platform or by state actors), downloading a video becomes an act of defiance. Whistleblowers, human rights monitors, and citizen journalists rely on downloader robots to create immutable copies.
are severe. A robot that intercepts traffic could, by design or accident, capture not just videos but also contact lists, location data, and message texts. Malicious versions of such robots have been used for espionage and stalking. Consequently, the same techniques that empower a journalist also empower an abusive partner.
Unlike YouTube or TikTok, which offer (sometimes grudging) built-in download buttons, WeChat treats most of its video content as ephemeral. Videos shared in “Moments” (the platform’s version of a timeline) or in group chats are often subject to automatic deletion, quality compression, or link expiration. It is within this frustrating gap between user desire and platform limitation that the concept of the emerges—not as a single device, but as a conceptual and technical solution designed to reclaim agency over digital content.
explicitly forbid “using any robot, spider, or other automatic device to access the service for any purpose.” Violation can result in permanent account bans. Tencent has also successfully sued developers of downloader bots in Chinese courts under anti-circumvention provisions of the Cybersecurity Law.
It reminds us that software is not fate. Behind every endpoint, every encrypted packet, every expiring URL is a person who wants to keep what they have made or been given. The robot does not merely download videos; it asserts that in the tension between ephemerality and permanence, the user should have the final word.



Got questions? We've got answers. If you can't find what you're looking for, feel free to reach out to our support team.